Below you’ll find breaking news as well as reports, updates on our campaigns, and victories.
If you are a member of the press, please reach out to [email protected]

Press Release
FIFA Sponsorship Deal with Saudi Aramco Covering World Cups Raises Human Rights Concerns
World football could be dogged by human rights violations unless action is taken to address Saudi Arabia's atrocious human rights record.
April 26, 2024

Press Release
Global: Loss and Damage Fund for Climate Change Must Not Restrict the Role of Civil Society
Full involvement of civil society would help reflect the views of the often diverse and marginalized communities whose rights are most affected by the climate crisis.
April 25, 2024

Press Release
US: TikTok Ban Won’t Solve Harms of Big Tech’s Invasive Surveillance
The U.S. government’s decision to impose an outright ban on TikTok fails to address the endemic human rights risks and harms associated with the surveillance-based business models of other tech companies, including Meta and Google.
April 25, 2024

Press Release
Amnesty International Urges University Administrations to Respect and Protect Students’ Rights to Protest
The right to protest is critical to freely speak out against what is happening right now in Gaza.
April 24, 2024

Press Release
Discovery of Mass Graves in Gaza Highlights Urgent Need to Grant Access to Independent Human Rights Investigators
The harrowing discovery of these mass graves underscores the urgency of ensuring immediate access for human rights investigators, including forensic experts, to the occupied Gaza Strip.
April 24, 2024

Press Release
Amnesty International Sounds Alarm on a Watershed Moment for International Law Amid Flagrant Rule-Breaking by Governments and Corporate Actors
Amnesty International launches its annual "The State of the World’s Human Rights" report, delivering an assessment of human rights in 155 countries.
April 23, 2024

Report
The State of the World’s Human Rights: April 2024
Amnesty International documented the state of the world’s human rights in 2023, connecting issues at global and regional levels.
April 23, 2024

Press Release
State-Backed Deadly Rampage by Israeli Settlers Underscores Urgent Need to Dismantle Apartheid
The failure to address these root causes and to hold Israel accountable for its violations of international law is enabling the continued dispossession and oppression of Palestinians.
April 22, 2024

Press Release
Syria: Mass Death, Torture and Other Violations Against People Detained in Aftermath of Islamic State Defeat – New Report
People detained in Syria after territorial defeat of Islamic State are facing systematic violations and deaths due to inhumane conditions.
April 17, 2024

Report
Aftermath: Injustice, Torture and Death in Detention In North-East Syria
The US government’s partner in northeast Syria is engaged in the large-scale and systematic violation of the rights of more than 56,000 people in its custody.
April 17, 2024

Press Release
Venezuela: Persecution Builds Relentlessly for Civil Society and Dissidents
Maduro’s government has started the year with an alarming intensification of the policy of repression that it uses to try to curtail civic space, critical voices and political opposition.
April 16, 2024
Press Release
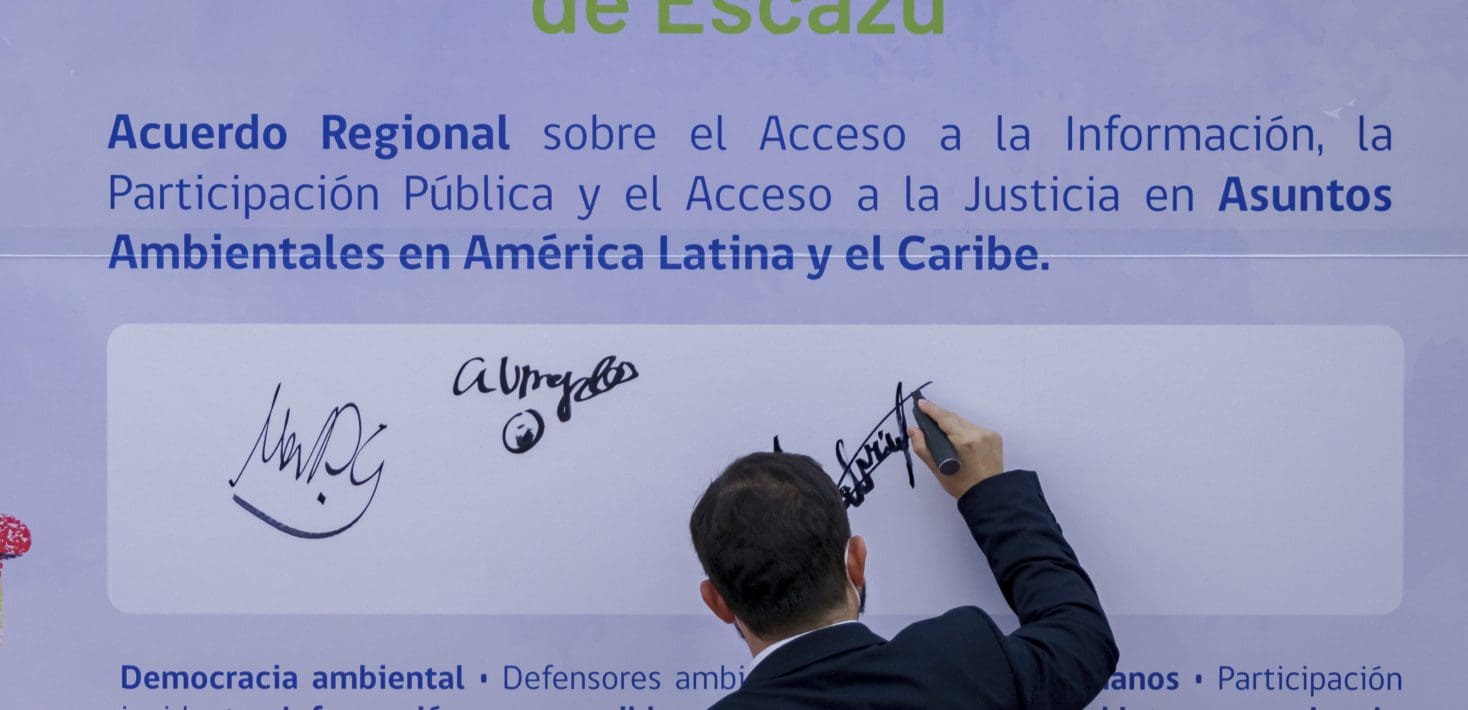
Americas: States Must Commit to Ending Violence Against Environmental Defenders
The Escazú Agreement is the first binding treaty in Latin America and the Caribbean that includes specific provisions for the protection of environmental human rights defenders.
April 15, 2024
